The Problem
MCP Creates an Attack Surface Traditional Security Cannot See
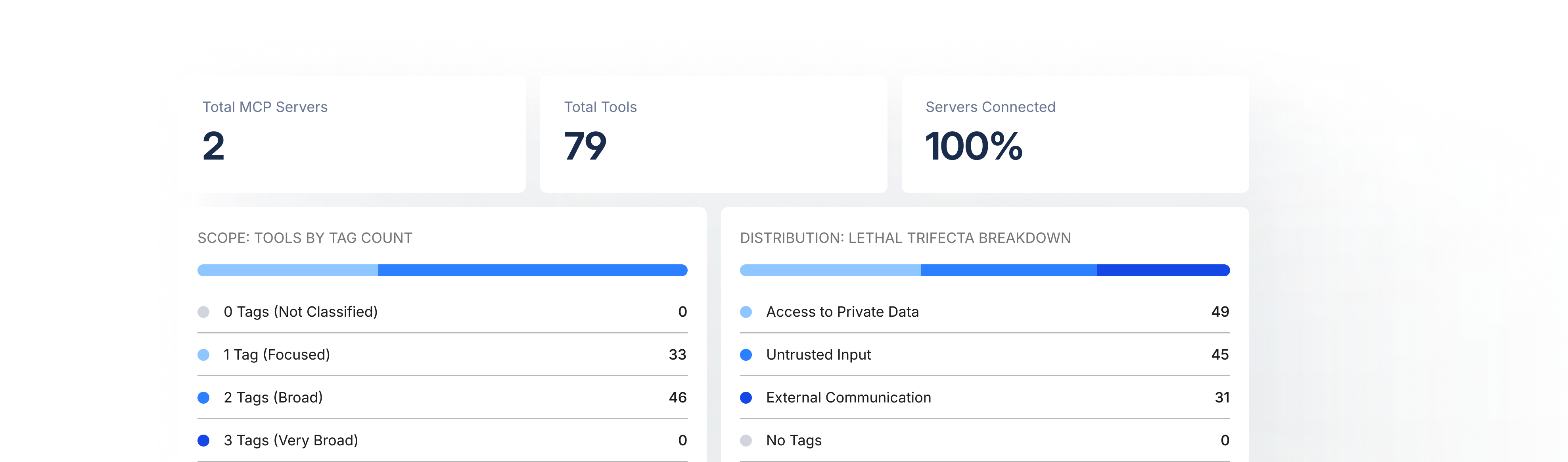
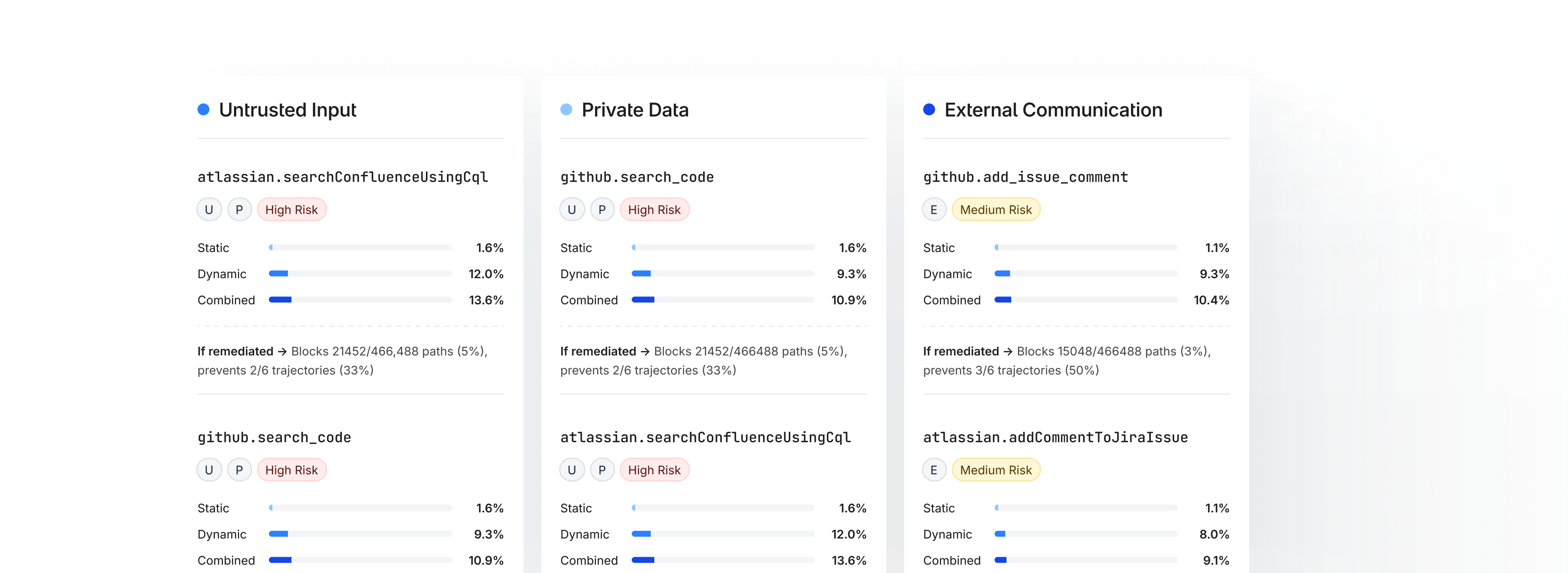
AI agents connect to enterprise systems through Model Context Protocol (MCP), exposing tools across Jira, GitHub, Salesforce, Slack, filesystems, and more. This surface is invisible to DLP, CASB, and SIEM tooling. The attack vector is not a single misconfigured tool. It is the combination.















.webp)
